IMAP Brute-Force Protection
IMAP Protection Overview
RdpGuard provides effective protection for your IMAP server against brute-force attacks. It does so by monitoring the IMAP port(s) or logs on your server and automatically blocking the attacker's IP address when the number of failed authentication attempts from a single IP address reaches a pre-set limit.
Follow the instructions below to learn how to enable and configure IMAP protection using RdpGuard.
To Enable and Configure IMAP Protection
Start RdpGuard Dashboard and click on the link next to IMAP
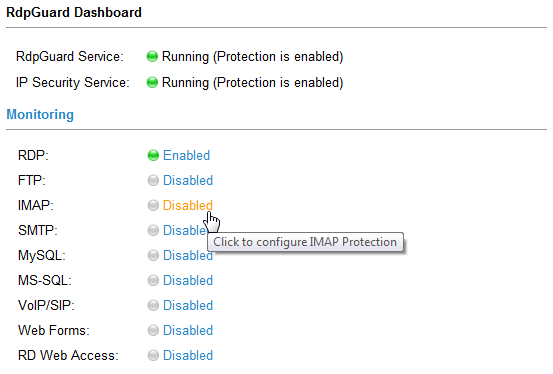 IMAP Protection Link in RdpGuard Dashboard
IMAP Protection Link in RdpGuard DashboardThe IMAP Settings dialog will open:
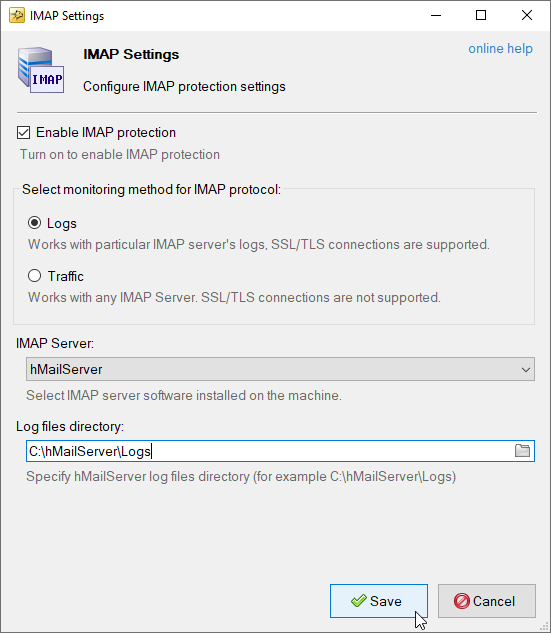 IMAP Detection Engine Settings
IMAP Detection Engine SettingsMonitoring method for IMAP protocol
The following monitoring methods are supported for IMAP protocol:
Log based monitoring
The recommended default option for IMAP monitoring is via Logs. This method works by monitoring specific IMAP server logs and is more resource-efficient than monitoring traffic. Additionally, it supports SSL/TLS connections and username detection.
IMAP Server
The following IMAP servers are supported for now:
Log files directory
Specify log files directory used by selected IMAP server.
Traffic based monitoring
The second option for IMAP monitoring is via traffic. This method works with any IMAP server, but uses more resources than monitoring via logs. It's worth noting that this method doesn't support SSL/TLS connections or username detection
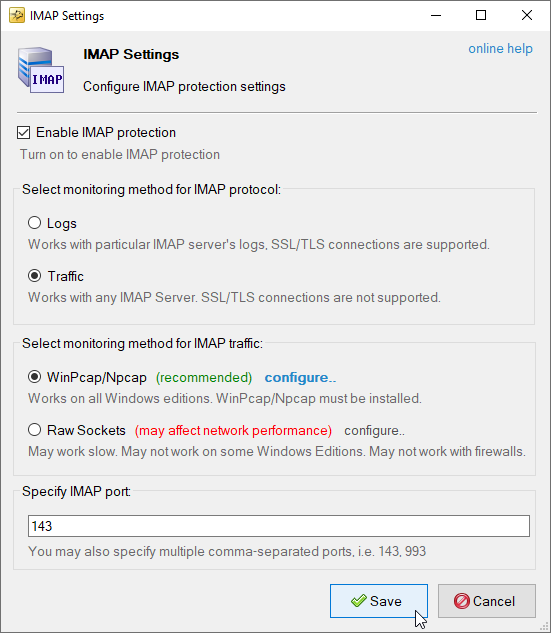 IMAP Monitoring via Traffic
IMAP Monitoring via TrafficThe following traffic based monitoring methods are supported
- WinPcap - Works on all Windows Editions, WinPcap must be installed.
- Raw Sockets - Does not work on Windows Server 2008 or with firewalls.
IMAP port
You can specify multiple comma-separated ports for IMAP traffic monitoring.
RdpGuard protects:
- Remote Desktop
- MS-SQL Server
- FTP Protocol
- HTTP Protocol
- IMAP Protocol
- POP3 Protocol
- SMTP Protocol
- IIS Web Login
- MySQL Server
- ASP.NET Forms
- RD Web Access
- VoIP (SIP Protocol)
- SSH Protocol
- MS VPN (RRAS)
"This sotware is really great. It's a relief. Because my server is constantly under attack. Thanks RdpGuard" - Joaquim De Sousa Marques
"Nice product. I used to implement something similiar in a low-tech and cumbersome manner via a script called TSBlock (not mine). This makes it much easier and is well worth the pricetag for SMB's." - J. Johnson
"Absolutely amazed at your product. We are a church in the North Dallas area, and I discovered this morning multiple failed logon attempts via our Remote Access Server. A friend suggested your product, so I immediately downloaded the trial. It had a list of about five blocked IP addresses in minutes, and that was enough to lead me to push the BUY button. Over the past 10-15 minutes the list is now about thirty with at least a third being international attempts to break into our system. Thanks for a great product. You may have just saved us much grief." - John Hallford
"Love the software. RDP on our Windows servers is just ridiculous. We would block it in the router but we have lots of old-time customers that would have issues." - Scott Hirsch
"Love the software! Makes it easier than tailoring VB Scripts!!" - Nick Brennan
"It's a great product - really stopping those RDP attackers :-)" - Dave, UK
"First of all: Your application is very (!!!) useful and I like it very much securing my 2012 R2 server. RdpGuard is the best solution, I found on the market and after 10 minutes of testing it I ordered the fully-featured version. :-)" - Carsten Baltes