Advanced Blocking Settings
Advanced Blocking Settings Overview
Starting from version 3.1.7 RdpGuard supports advanced blocking settings providing you the way to define how attackers' IP addresses are blocked.
Earlier versions of RdpGuard block all access to the server when the number of failed login attempts from a single IP address reaches a set limit.
In some cases you may want to block only particular ports, for example RDP, FTP, SMTP while leaving others accessible, for example HTTP or HTTPS.
This can be configured via Advanced Blocking Settings.
How to configure Advanced Blocking Settings
1. Click Tools, Options
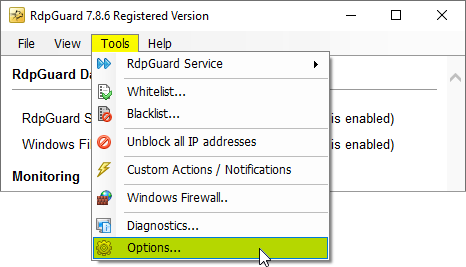 Click Tools, Options
Click Tools, OptionsThe Options dialog will open:
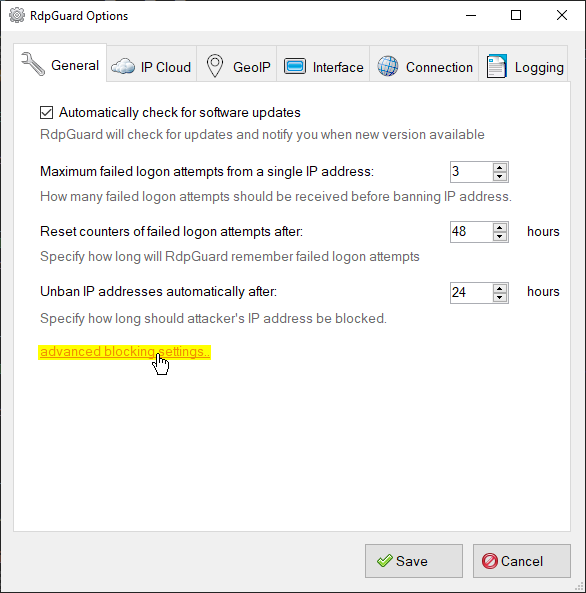 RdpGuard Options dialog
RdpGuard Options dialog2. Click Advanced blocking settings..
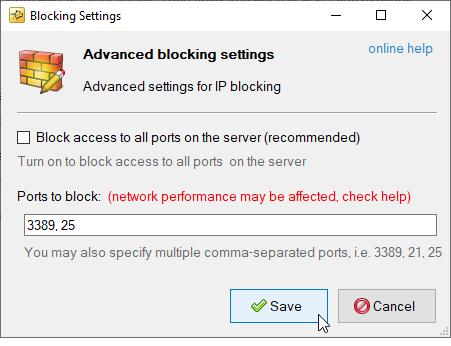
The Advanced blocking settings dialog will open:
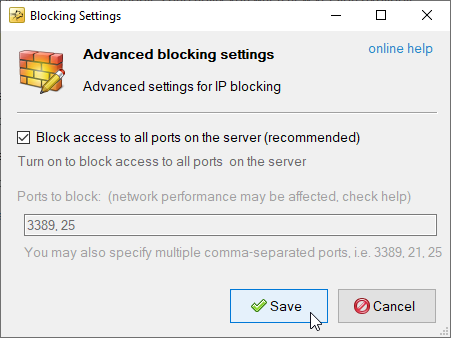 How to block access to all ports
How to block access to all ports3.a. If you would like to block access to all ports on your server (i.e. make your server invisible to the attacker), tick the Block access to all ports on the server checkbox and click Save
3.b. If you would like to block access only to particular protocols, untick the Block access to all ports on the server checkbox and specify the ports you want to block when the number of failed logon attempts reaches a set limit.
 How to block only particular ports
How to block only particular ports4. Click Save
Performance Considerations
Things to consider when blocking multiple custom ports: if you would like to block multiple ports like shown on the screenshot above, please note that this will increase the number of conditions added to the Windows Filtering Platform proportionally and may affect network (and overall) performance.
When you block all access to the server (the Block access to all ports on the server checkbox ticked) - one condition is required to block one IP address.
But everything changes when you block specific ports, like 3389, 21, 25, 110. The number of conditions added to Windows Filtering Platform increases proportionally:
Conditions per one IP = Number of Ports [TCP] + Number of Ports [UDP]
For example, blocking 1000 IP addresses from accessing all ports on a server requires 1000 conditions in the Windows Filtering Platform. When you block access for the same 1000 IP addresses to 4 ports (for example, 3389, 21, 25, 110) - 8000 conditions are added to the Windows Filtering Platform (4 for TCP and 4 for UDP), which can have a greater impact on network performance.
The number of conditions added in the Windows Filtering Platform affects the network (and overall) performance of your server, so we recommend leaving the Block access to all ports on the server option enabled and the default blocking period of 24 hours to reduce the number of blocking conditions.
RdpGuard protects:
- Remote Desktop
- MS-SQL Server
- FTP Protocol
- HTTP Protocol
- IMAP Protocol
- POP3 Protocol
- SMTP Protocol
- IIS Web Login
- MySQL Server
- ASP.NET Forms
- RD Web Access
- VoIP (SIP Protocol)
- SSH Protocol
- MS VPN (RRAS)
"This sotware is really great. It's a relief. Because my server is constantly under attack. Thanks RdpGuard" - Joaquim De Sousa Marques
"Nice product. I used to implement something similiar in a low-tech and cumbersome manner via a script called TSBlock (not mine). This makes it much easier and is well worth the pricetag for SMB's." - J. Johnson
"Absolutely amazed at your product. We are a church in the North Dallas area, and I discovered this morning multiple failed logon attempts via our Remote Access Server. A friend suggested your product, so I immediately downloaded the trial. It had a list of about five blocked IP addresses in minutes, and that was enough to lead me to push the BUY button. Over the past 10-15 minutes the list is now about thirty with at least a third being international attempts to break into our system. Thanks for a great product. You may have just saved us much grief." - John Hallford
"Love the software. RDP on our Windows servers is just ridiculous. We would block it in the router but we have lots of old-time customers that would have issues." - Scott Hirsch
"Love the software! Makes it easier than tailoring VB Scripts!!" - Nick Brennan
"It's a great product - really stopping those RDP attackers :-)" - Dave, UK
"First of all: Your application is very (!!!) useful and I like it very much securing my 2012 R2 server. RdpGuard is the best solution, I found on the market and after 10 minutes of testing it I ordered the fully-featured version. :-)" - Carsten Baltes